US English Female Voice
US English Male Voice
UK English Female Voice
UK English Male Voice
LISTEN TO AUDIO, READ, OR BOTH?
The audio broadcast is posted for your listening pleasure, it is the same as what you can read below. Listening, listening while reading, for some, this is like being in front of a college professor giving a lecture and is a great way to learn. And others like to only read. Whatever works for you, both are available.
ABOUT THIS CHAPTER
This Chapter is more techie than most of the others. It will be great proof to you, I hope, you can understand an important computer topic if it is presented properly, slowly and methodically, and logically, and simply.
This Chapter is super important for your computer’s security, truly the number one, numero-uno, security measure you should take. My Case Study article is about a real-life situation and a computer’s files being saved from DISASTER because of the system being properly setup according to this Chapter. Which was luckily done just two days prior to the event.
If you follow through this Chapter and don’t fully understand it, but are able to do what it says, that is, just follow a few simples directions, that is all you really need to get out of Chapter 01. I would love for you to fully understand it, and I’m going to try and keep things simple, but please don’t be discouraged and not read the rest of this book if this Chapter has you feeling a little lost. This one is more about importance and just following some directions than it is about fully understanding every little piece of it. Don’t be scared, just letting you know in advance.
Chapter 03 on passwords you’ll find pretty simple and Chapter 04, which helps you implement what you’re about to learn in this Chapter, I promise, will be the last super-techie thing for a while. I take system security really seriously, so I want to get this more complicated stuff out of the way so we can have some fun learning more useful day to day stuff, running safely.
This Chapter is actually a great test for both of us. My test is to see if I can present this topic in really simple terms. And your test is did you understand it? If either test gets a flunking grade, that’s a reflection on me, I’m the one who will get the bad report card, not you.
Throughout this book, I stress that my providing answers to your questions is the key to your never being frustrated when learning new computer topics. If you feel confused and choose to not read the rest of this book, which has much more interesting topics than this first one, in the words of the immortal Dan Aykroyd, it would really bummer me out.
NO CONFUSING TERMS
I’ll explain terms as I go. Some of these terms you may think what is this guy kidding? of course I know what that is. But not everyone will know exactly what all terms are. I’m about to give a definition of desktop which you may think is really basic. When this happens, just skip to the next heading, or read the quick definition to see if you pick up anything new and helpful. I don’t want to bore you with really simple stuff and at the same time, I want to teach really simple stuff. I call some of this tip-bits™. You like that phrase tips-bits™? I made it up.
WHAT IS YOUR DESKTOP
Just curious, could you actually tell someone what your desktop is?
Your desktop is what you see on your computer’s screen when no programs are open. You turn on your machine, log in, and you are presented with your desktop. It includes your program icons, your Start Menu where you find all of your programs listed, and basically everything that is visible on your monitor is your desktop. A web browser such as Chrome™, Edge™, Firefox™, Brave™, Safari™ or one of many others, are computer programs. If you were to open your web browser to get to a website, that is now a program running on your desktop.
Even your phone’s screen is a desktop. When you have a program open, the program’s display window is not your desktop, the program is being displayed on your desktop. Even your text messaging app is a program running on your phone’s desktop. Remember, don’t understand something, even on something like what your desktop is, use the Comment section at the bottom of this page to send me your questions.
LETS RUN A PROGRAM: PTT911T.exe – IT WILL TELL US A LOT
We’re going to start by finding out a critical piece of information about how you run your own computer. The next few steps will have you download a very small computer program that will tell us what type of user you are on your computer. We’ll want this for the rest of the Chapter. Don’t worry yet about what I mean by what type of user. Lets find out first what type you are.
This program was written by me so I promise you it is safe to run on your system.
Lets start by clicking the button to download the PTT User Type Test program
Chrome browser and possibly others may give you a warning message about a suspicious or possibly dangerous download. You may ignore these warnings, they are expected (this is only a temporary problem):
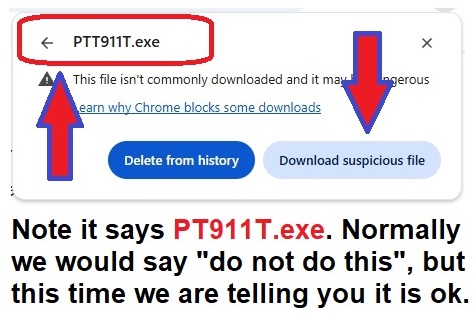
You will see a screen similar to the one below.
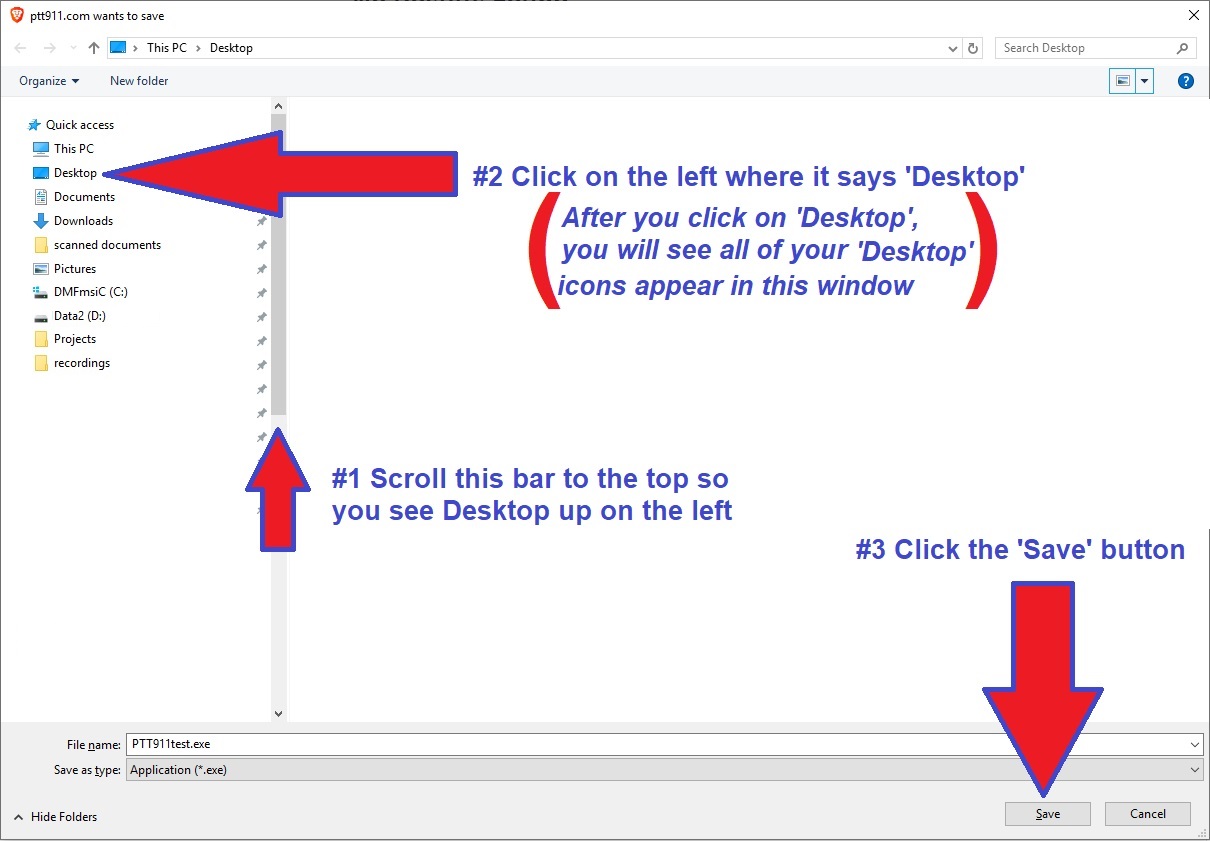
#1) On the left, scroll the grey-bar to the top and you will see ‘Desktop’ on the left.
#2) Click your mouse 1-time on ‘Desktop’.
#3) At the bottom, click ‘Save’.
This will SAVE the program PTT911T.exe to your ‘Desktop’
On your desktop you will see its program icon like the picture below:
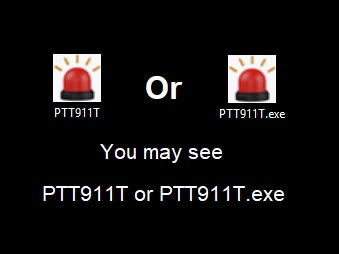
You will now see this new icon on your 'Desktop'. It may say PTT911T or PTT911T.exe
A future Chapter will explain why you may or may not see the “.exe” displayed. In that Chapter, I’ll explain why I prefer you do see the .exe. It helps security if you see that part of a file name called the file-extension as it tells you what type of file it is. Pictures, programs, music and all other files each have their own file-type-extension. If you only see the name PTT911T with no file-type-extension, you won’t necessarily know if it is a picture such as PTT911T.jpg or a potentially dangerous program PTT911T.exe. I’ll go over this in detail in a future Chapter. And note, PTT911T.exe is safe.
Double-click on the new PTT911T desktop icon to run the test program
When you see the screen below, click on the option that says ‘More info’
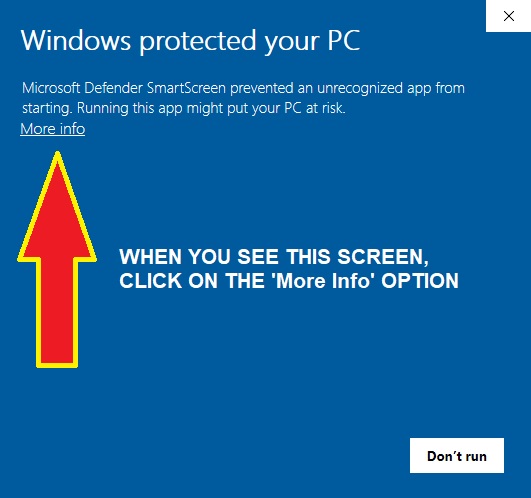
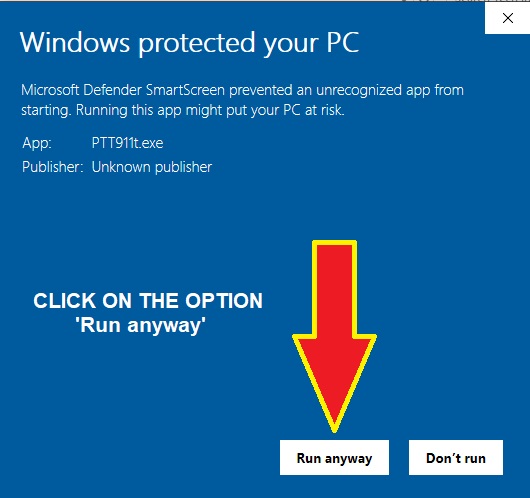
On the next screen, shown below:
Click on the option that says ‘Run anyway’
LETS SEE IF YOU ARE A STANDARD USER OR AN ADMINISTRATOR
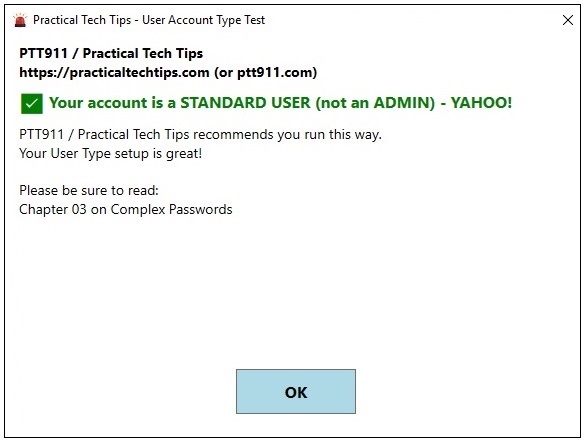
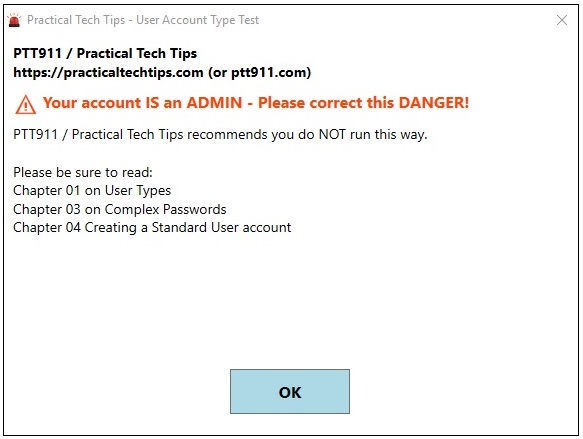
The PTT911T program will tell you what type of user you are, a STANDARD USER or an ADMINISTRATOR . You will see one of the two screens below.
A QUICK WORD TO THE TECHIES
If you’re a real techie you’ll most likely understand right away where I’m going in this Chapter. You probably still won’t do anything about it because you won’t think it’s necessary, but hopefully this Chapter convinces you otherwise and you run the way I run my own system. For the record, in over 40 years of running Microsoft™ operating systems, I have yet to ever get a virus. And if still not convinced, read my Case Study article. And feel free to share the PTT911T program with others, it a handy little utility.
DO I REALLY NEED TO WORRY ABOUT ALL OF THIS? YES! YES! YES!
By the end of this Chapter, I believe you’re going to say “WOW, I really need to do this, I must be sure my system is running more securely”. I’m going to teach about a security issue you probably never knew existed. By the end of the Chapter, you’re going to realize that it doesn’t matter the topic was a little techie sounding as you’re going to understand its importance.
SECURITY IS SUPER IMPORTANT
We all fear security problems, viruses, identity theft and all of the other dangers we face. Having our computers connected to the Internet and being on websites like our online banking, Amazon™ and social media sites such as facebook™, makes security our number one priority. So lets work together to make your system more secure. A great part about this, other than taking a short amount of time, there is no cost to this, no need to buy anything. Everything you need is built right into Windows™. I’ll continue to address security issues throughout this book whenever it’s relevant to the topic.
PASSWORD OR NO PASSWORD
The first step to system security is having a password and making sure it is long and complex, both of which are explained, simply, in Chapter 03.
When you first turn on your computer, does your system ask for a password?
If your system does not require a password, this is the equivalent to leaving the door of your car unlocked, the windows down, a full tank of gas, and the keys in the ignition.
If you have no password, or what may be a weak password, like a single lower case word with just one number, please be sure you read Chapter 03 on passwords and Chapter 04 tells you how to change your password.
WHAT IS A USER
You use your computer and your computer refers to you a user. If more than one person shares the same computer, each would be their own user with their own username. And the PTT911T program told you what type of user you are, a STANDARD USER or an ADMINISTRATOR.
Think of a factory with an office area. You work in the factory yet have your own private office. Think of your computer as being the entire factory and your private office is like being a user.
Your office has a filing cabinet with drawers, each holding a specific type of information.
As a user, Windows™ provides you with a special area for your files such as your documents, music, pictures and other file types. Each file type has its own special area, similar to a drawer in the filing cabinet. So your documents are in one drawer and your pictures are in another.
This way, everything of importance is together in the filing cabinet and by having each type of information in its own filing cabinet drawer, it makes organizing and finding things easier.
I’m sure you’ve seen your DOCUMENTS folder. The DOCUMENTS folder is one of these special places, one of the drawers in your filing cabinet. If you had other users on your computer, each user would have their own filing cabinet. Your filing cabinet is linked to you as a user.
The system provides you with a filing cabinet of your own called your Home Directory or User Profile Area. Don’t worry about remembering that name. If you use a program like Word™ or Excel™ to create documents and spreadsheets, these get stored in your DOCUMENTS folder. Music gets stored in your MUSIC folder, pictures in your PICTURES folder and if you download something from a website it will go into your DOWNLOADS folder. There is also your DESKTOP which is a special folder. Anything you put in your desktop folder will automatically show on your screen, on your desktop. Each of these is a drawer in your personal filing cabinet.

This shows your private Windows™ area, or your Home Directory / User Profile Area
NOTE: Did you know you can view your desktop in File Manager as if it were a folder of files?
We’ll get to this in a later Chapter, it’s makes for a really easy way to clean up your desktop
Having this organization also makes it easier to find what you need to backup for safe keeping. A later Chapter discusses backups and how to make them.
THERE ARE 2 TYPES OF USER YOU NEED TO KNOW ABOUT
There are many different types of users but you only need to know about two of them, a STANDARD USER and an ADMINISTRATOR. Each type has different powers.
A STANDARD USER has Standard power. Can do standard things.
An ADMINISTRATOR has Super power. Can do great things, and a lot of damage.
A STANDARD USER is the equivalent to being a hotel guest with a key to just one room and the use of some facilities such as the pool and laundry. The equivalent on your computer is your hotel room is like your Home Directory where your DOCUMENTS and other folders are, this is your private area. Being a guest at the hotel, you have a right to use the pool and laundry. As a STANDARD USER, you are given the right to use your computer’s resources such as printers, scanners, speakers and microphone.
If you lose your key, a criminal can only get into your one small hotel room and not the entire hotel. A hacker getting into a STANDARD USER gives them very little power. A hacker can do damage within your private area but it is very hard to penetrate areas you don’t have a key for.
An ADMINISTRATOR is the equivalent to being the hotel manager, the one with the master-key to the entire hotel. That’s the equivalent to having access to your entire computer, including areas you rarely, if ever, need to touch, like your operating system. And if other people share your computer, an ADMINISTRATOR can access their private areas as well, their filing cabinets.
ADMINSTRATORs can get into everything on the computer. In the wrong hands, such as those of a hacker getting into an ADMINISTRATOR account, is like losing the hotel’s master-key. This makes your entire computer susceptible to bad things happening such as viruses, ransomware and many other types of malicious behavior. Some bad things can happen to a STANDARD USER but it is much harder to do major damage without being an ADMINISTRATOR.
So what does all of this mean in English?
You should be running your own computer as a STANDARD USER and not as an ADMINISTRATOR. Chapter 03 will help you create complex passwords, and Chapter 04 will help you make simple changes to your system so you run safely as a STANDARD USER.
Most people run as an ADMINSTRATOR. When a computer is purchased, a knowledgable technician does jump out of the box and tell you how to properly setup your system. You just followed the on-screen directions and it made you an ADMINISTRATOR without saying “ok, now go create another user account as a STANDARD USER and use only that one.” Another problem I run into, even good technicians were never taught this MOST IMPORTANT security tip-bit™, or just overlook it.
Running as the proper user-type, being a STANDARD USER, and some general knowledge discussed throughout this book on how to spot a threat, is your strongest defense against your computer system being invaded.
Now I’m a really advanced user, I know how to check if an E-mail is dangerous spam, I know when not to click on a potentially dangerous link, I know to not open E-mail attachments that may be dangerous, and you know how I run? As a STANDARD USER.
If something bad happens to an ADMINISTRATOR account, the entire computer is at risk and will usually have to be completely reloaded from scratch, even your programs will have to be reinstalled, everything can get lost.
If running as a STANDARD USER and something bad happens, like the hotel room key, only your small area, can be destroyed. You may need to do some work and restore files from a backup, but you can be back running in a very short amount of time, and not in two or three days after many hours of work reloading your system which may need professional help to do.
If you want to read a real life story, read our Case Study where a user luckily was setup properly. He still had system damage, but it was limited.
CHECK POINT
This is a good check point. If anything you have learned so far seems confusing or you have questions, this is a good time to stop and catch up, don’t continue. Reread if needed, listen to the audio, maybe listening while reading will help get past any rough spots. And always know you can ask question! I really don’t mind questions and I truly encourage them when they are needed.
It’s best to understand each section and don’t let confusion build, it only leads to frustration. And we don’t want any frustration. The whole point of this book is for you to learn some great tech tips, and not become frustrated. I’ll try to point out good places, like this, to be sure you’re good before continuing to the next topic. And remember, this first topic is not a simple one, it’s an important one.
There isn’t much more to go.
What can an ADMINISTRATOR do a STANDARD USER can’t?
Remember all that talk how STANDARD USERS can’t do everything and don’t have access to everything like an ADMINISTRATOR? Remember, ADMINSTRATORs have super-power.
When only an ADMINISTRATOR is allowed to do something, it’s called requiring Elevated Privileges. Only an ADMINISTRATOR is allowed run with Elevated Privileges.
A STANDARD USER is not allowed to do what requires Elevated Privileges.
Only an ADMINISTRATOR has the hotel’s master-key, and there are things the system won’t let you do with a standard hotel room key. That master-key is like having Elevated Privileges, you’re allowed to do about anything you want, go where you want, damage what you want, right or wrong, good or bad, the master-key does not question authority, it just allows total unrestricted access.
If you are a STANDARD USER and you do something that requires Elevated Privileges, your system is actually going to tell you. It will literally stop, your desktop will go dark, and a screen will pop-up asking for your ADMINISTRATOR password. Here’s a picture of what it looks like:
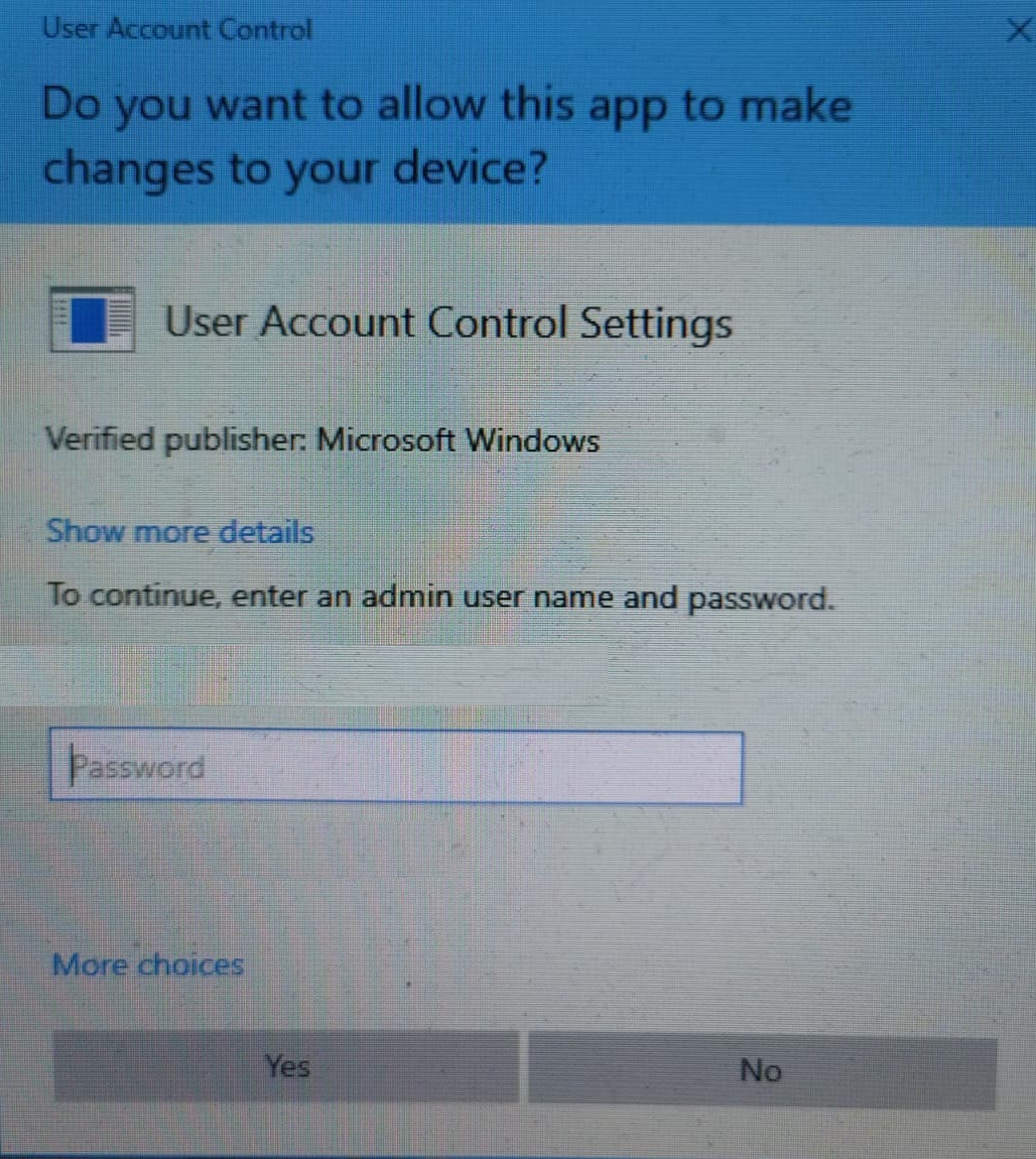
If you are properly running as a STANDARD USER, if you try to install a new program or update a program, that is, you do something that requires Elevated Privileges that only an ADMINISTRATOR has, the system will tell you and it will ask you for the ADMINSTRATOR password. This is a great safety mechanism since you can’t accidentally do something only an ADMINISTRATOR, with Elevated Privileges, can do without entering a password. You are forced to stop and think about it.
RECAP
Running your everyday programs should never require an ADMINSTRATOR with Elevated Privileges, it’s a really rare to need them. If you are a STANDARD USER and you install a new program, update an existing program, or try to do something only ADMINISTRATORs are allowed to do, that is, something that requires Elevated Privileges, the system will tell you, it will stop everything it’s doing, your screen will go blank, and you will be asked for the ADMINISTRATOR password. Not rocket science, it lets you know.
You know there are two types of users, STANDARD USER and ADMINISTRATOR.
And the PTT911T program, which hopefully you downloaded and ran, told you if you are running as a STANDARD USER or as an ADMINISTRATOR.
CONCLUSION
Chapter 02 is for those who share their computer with other users. If you are the only user of your computer, after finishing this Chapter, continue with Chapter 03 which will help you understand passwords and then Chapter 04 which will help you setup your ADMINISTRATOR and STANDARD USER accounts properly. You are getting past your first and most important security lesson!
I bet you’re feeling a little surprised right now that you just read all this new tech stuff and you probably feel you actually understood it, at least mostly. And mostly is pretty good, but still, if you have questions, don’t hesitate, let me know, I’m happy to answer them.
YOU ARE DOING GREAT! And remember, ask questions, it makes me happy to know you understand what I’m teaching. I know I told you at the beginning to not worry if you don’t fully grasp this Chapter, but I was only kidding, I didn’t want you to feel intimidated it would be over your head. If you didn’t understand something, please use the Comment form below and ask a question. No, you really don’t have to have grasped this Chapter 100%, but I prefer you do.
QUESTIONS & ANSWERS
Have a question on this Chapter? See the section below, ‘Submit a Comment’. Chances are, someone else probably has the same question. And, I may see a question and realize I need to simplify or rewrite something for clarity. Since this is not a hard printed book, updates are easy.
Always remember:
“There are no silly questions, only silly answers.
And an answer without a question is only a statement”.
Mayor Adam West™
If you share your computer with others, kids, significant other (subscribers only):
Chapter 02 – Setting up a computer for use by more than 1 user
Otherwise, continue to:
Chapter 03 – Creating a Complex Password
